Lockdown Mode Past and Present
vSphere 6 introduces changes to Lockdown Mode and the DCUI overall to provide more granularity and flexibility. In the past (5.5 and before), lockdown mode was disabled by default and if enabled, users could not log in directly to the esxi host nor could they use SSH even if SSH was enabled. If the vCenter was not available, root had to disable Lockdown Mode in order to connect to the esxi host via the vSphere Client.
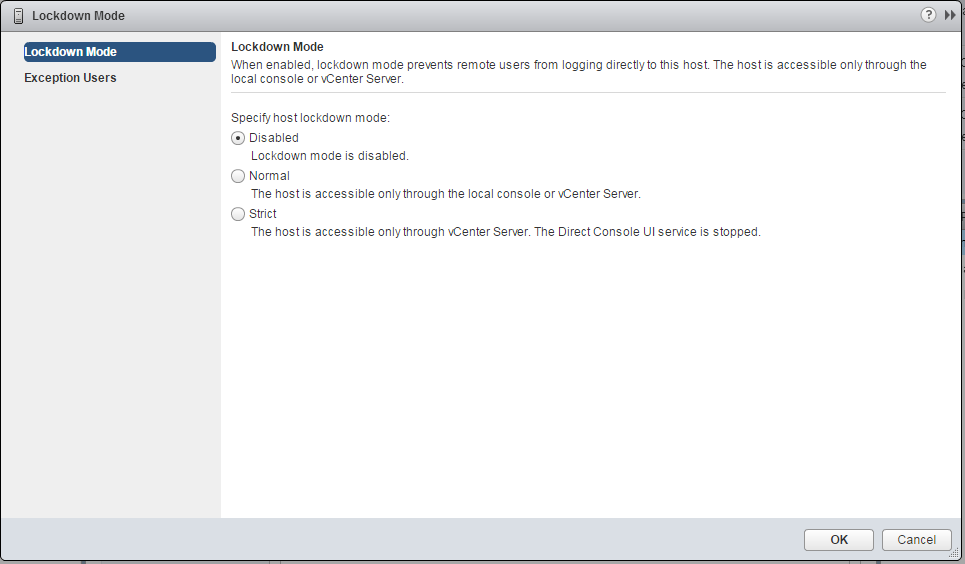
vSphere 6 not only has the disabled (still the default) and enabled mode but introduced new choices. If enabled, lockdown mode could be set to Normal Mode or Strict Mode. In Normal mode, privileged
users can log into to the esxi host using the vsphere client or use the DCUI. In strict mode, the DCUI
is turned off but those privilege users can still log into the esxi host using the vSphere Client.
Here are some captures:
1. This is the default.
2. These are the choices.
3. If Enabled via Normal mode, this is what you see. As is, nobody can launch the vSphere Client and successfully connect to the esxi host directly. Yet, the dcui is still available.
4. If you decide to change it to Strict Mode, you get this warning. Before you do this, you may want to create a list of Exception Users.
5. vSphere 6 introduces the ability to create a list of Exception Users. These users will still have access to the esxi host via the vSphere Client if the vCenter Server is unavailable. To do this click on Edit to add the valid user with permissions. Domain accounts can be added to this list.
6. Notice the next two captures. The user is able to log in directly to the esxi host in both Normal and Strict Mode.
7. Despite the fact that those users can log in the esxi host via the vSphere Client, the DCUI is not running in Strict Mode. This is what you see in vSphere 6 if Lockdown Mode is in Strict Mode.
Note: http://blogs.vmware.com/vsphere/2015/03/vsphere-6-0-lockdown-modes.html
Lockdown Mode and the ESXi Shell and SSH Services
Strict lockdown mode stops the DCUI service. However, the ESXi Shell and SSH services are independent of lockdown mode. For lockdown mode to be an effective security measure, ensure that the ESXi Shell and SSH services are also disabled. Those services are disabled by default.
When a host is in lockdown mode, users on the Exception Users list can access the host from the ESXi Shell and through SSH if they have the Administrator role on the host and if these services are enabled. This access is possible even in strict lockdown mode. Leaving the ESXi Shell service and the SSH service disabled is the most secure option.